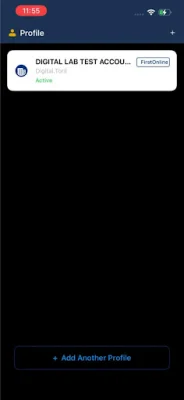

FirstToken Corporate
by FirstBank Nigeria (0 Reviews) April 18, 2026Latest Version
April 18, 2026
FirstBank Nigeria
Finance
Android
0
Free
com.gedutechnologies.corporate
Report a Problem
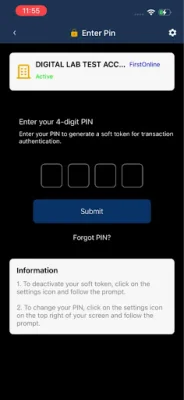
More About FirstToken Corporate
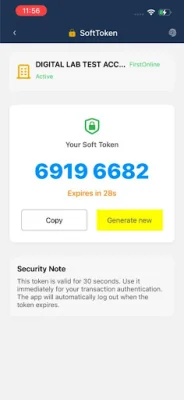
This application is designed to provide secure and efficient access to internal systems for corporate users. It offers a range of key features that make it a valuable tool for businesses looking to protect their data and streamline their onboarding process. One of the most important features is the ability to instantly generate authentication codes, ensuring that only authorized users are able to access sensitive information. This helps to prevent unauthorized access and protect against potential security breaches.
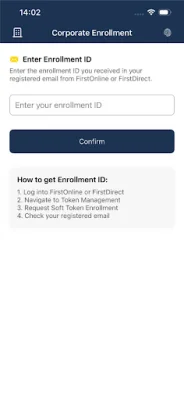
Another key feature of this application is its streamlined onboarding process. With a unique Enrollment ID, users can activate their profile in a matter of seconds, making it quick and easy to get started. This eliminates the need for lengthy and complicated onboarding procedures, saving time and resources for both the user and the company.
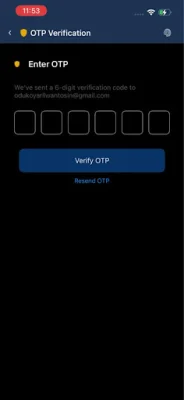
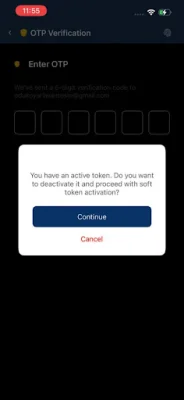
In addition to these features, the application also offers Multi-Factor Authentication (MFA), which adds an extra layer of protection to corporate data. This means that in addition to a password, users will need to provide another form of authentication, such as a code sent to their phone, to access the system. This helps to prevent unauthorized access even if a password is compromised.
One unique aspect of this application is its ability to provide offline access. This means that even without an active internet connection, users can still generate secure tokens after their initial enrollment. This is especially useful for employees who may need to access sensitive information while traveling or in areas with limited internet access. It ensures that they can still securely access the system without compromising its security.
In summary, this application offers a range of key features that make it a valuable tool for businesses looking to protect their data and streamline their onboarding process. With instant token generation, streamlined onboarding, MFA, and offline access, it provides a robust and secure solution for corporate users. By utilizing this application, companies can ensure that their data remains protected and accessible only to authorized users, helping to prevent potential security breaches and maintain the integrity of their systems.
Rate the App
Popular Apps